Today we take a look at how to secure your WordPress website in 2016. In a previous life I sold Enterprise Content Management Systems. The word “enterprise” is important here. Enterprise usually meant (and to a large degree still does mean) WordPress wasn’t even considered. Despite the fact that WordPress powers just over 26% of the entire fricking web, there is still a perception in large corporate and government organisations that WordPress is a little play toy that’s best used for non-critical blogs and smaller websites. As I became immersed in the world of WordPress and began to introduce it as a real, viable alternative to Enterprise CMS platforms (some of which came with a price tag of well over $100,000 in license costs alone!) I found myself having to challenge this perception and convince clients used to spending large amounts on Enterprise CMS implementations that WordPress could reduce their implementation costs AND be an overall better solution to their content management requirements.
Is WordPress secure?
Contents
By some considerable distance, the number 1 reason I heard from enterprise clients why the didn’t want to use WordPress was that they believed that it was a hackers dream.
“WordPress is not secure”,
“I heard sitex.com was recently hacked and they run WordPress”,
“WordPress is for amateur websites – we can’t trust it given the number of security issues we hear about”.
These were the kind of statements I would hear on almost a daily basis. It’s a stigma that I believe still hinders the growth of WordPress in many organisations across the globe. Are they right?
In short – no. WordPress is secure. Very secure. In fact, I would argue it may be one of the most secure pieces of software in the world at this point.
No other piece of software is subjected to as much scrutiny as WordPress is. Think about it.
- The source code is 100% open source, meaning any hacker can spend their time studying the WordPress source code on a daily basis hunting for vulnerabilities. Most enterprise Content Management Systems (and most hosted content management systems) are closed source applications meaning hackers have no direct access to their source code. They are somewhat protected by obscurity. If many of these applications were to suddenly go open source one could imagine their first major contributions would be security patches.
- WordPress market share (26.4% in May 2016) dwarfs everything else by considerable distance (Joomla is no.2 at just 2.7%). Simply by virtue of the fact that there are millions more WordPress websites than anything else, WordPress is subject to way more attacks than anything else. This global web scale means WordPress has benefited from a scale of threat assessment and vulnerability testing that I think is unprecedented.
When you combine the popularity of WordPress and the complete transparency of it’s source code you have the potential for the perfect storm if your software is not very very secure. In fact, you’re quickly forced to become very secure – otherwise people would leave you in their droves.
If WordPress is so secure why do so many think it is not?
How many road deaths where there by drivers of supercars in 2015? Probably not a lot. How many road deaths were there by drivers of 4 door sedan cars? Probably millions globally. Are 4 door sedan cars more dangerous than supercars? Of course not, there’s simply way fewer supercars out there. It’s the same with WordPress. While the software itself is very secure, how people frequently use it is a whole other ballgame. You have good 4 door sedan drivers and you have inexperienced, irresponsible and stupid 4 door sedan drivers.
The ubiquity of WordPress means it’s used by everyone from Beyonce, The Rolling Stones to your moms cat blog. It is also the platform of choice for every single shitty spam blog on the planet. You’ll quite frequently hear about smaller WordPress websites getting hacked regularly. But how many times have you heard about Beyonces website getting hacked? Or The Rolling Stones website for that matter? What about the Microsoft blog or the New Yorker? If WordPress wasn’t so secure wouldn’t these websites also be getting hacked all the time? Here’s the major reason why WordPress has an unearned reputation for shitty security – it’s not the software itself – it’s the people using it.
What are the big guys doing differently? On a self hosted instance of WordPress, WordPress itself is only one part of the equation. Let’s take a look at the most important things that you can do to secure your website so protected from the majority of reasons why WordPress websites get hacked.
Here’s how to secure your WordPress website in 2016
Use quality WordPress hosting
The is the big one. Millions of WordPress websites are hosted on crap hosting providers. Crap hosting providers usually either don’t know or don’t care about how to harden their servers to common attack vectors for WordPress and php applications in general. More important they’ll allow users to do stupid things like granting global read/write/execute permissions on entire directories (seriously if you’re doing this stop right now and go and change this RIGHT NOW. I don’t care if you think you need it for your site to work. You don’t. There’s a better way – trust me.) Get yourself a decent webhost who truly understands WordPress like Siteground. A decent host will protect it’s servers with multiple firewalls – both hardware and software based.
Keep WordPress up to date
This is not optional. WordPress is open source remember. This means that when a new vulnerability is found you’ll have thousands of attacks scouring the web looking to exploit this. WordPress has a stellar record as pushing out fixes for vulnerabilities as soon as they’re discovered and reported. As long as you’re auto updating WordPress to accept new versions you’ll protect yourself from one of the big reasons why smaller WordPress websites get hacked. Automatic updates for minor WordPress updates are enabled by default in WordPress. I would also recommend switching on automatic updates for major releases. This can easily be done by adding a single line to your wp-config.php file.
define( 'WP_AUTO_UPDATE_CORE', true );
Learn more about Automatic updates.
Keep themes and plugins up to date
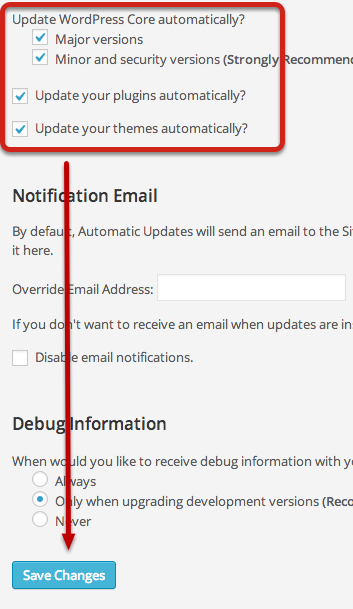
WordPress makes it so easy to keep it updated that quite often exploit attacks are most likely to be found in out of date themes and plugins. It’s possible to configure WordPress to automatically update themes and plugins but it requires a little more effort. There are a few ways to do it. The simplest way is to install and configure the Advanced Automatic Updates plugin.
The other way to do this is to use WordPress.com via Jetpack to turn on Autoupdates for plugins. We’ll be back with a dedicated tutorial on this tomorrow.
Do I need a security plugin?
Honestly, the actions above will most likely protect you from most bad actors in the WordPress ecosystem. Tons of people spend hours installing tons of security plugins for WordPress but still run their website on shitty hosts and run out of date versions of WordPress and various plugins and then wonder why they’re being hacked. Get the fundamentals right and you’re 95% of the way there. The above recommendations are non-negotiable – you NEED to do these things. Beyond that I think there is value from additional layers of security, but they are only useful if you’ve first got the fundamentals right. There are tons of WordPress security plugins and I’m not going to get into the ins and outs of each one today. Right now, if you want to use one I recommend WordFence. There’s very little between the main players like iThemes Security, Sucuri Security, and All in One WP Security. I personally prefer WordFence simply because it provides a real time scanner for free whereas mos of the others charge for this. The other plugin I really like is Ninja Firewall which is a full Web Application Firewall.
If you run your own VPS/Dedicated server and use Apache as your web server I would also recommend you configure the free Modsecurity ruleset from Comodo. I’ve generally found them to be way better than the default ruleset that comes with many cPanel servers.
Protecting WordPress Admin from Brute Force login attempts
Protecting your WordPress admin is the one other thing I suggest you do in addition to the recommendations above. Give Clef Two-Factor Authentication a shot.